Understanding site to site VPNs: A Practical Guide to Secure Business Connectivity
Quick fact: Site-to-site VPNs securely connect multiple networks over the internet, enabling private communication between offices as if they were on the same LAN.
Site-to-site VPNs are the backbone of many growing businesses, letting multiple offices share resources securely without exposing them to the public internet. In this guide, you’ll get a clear, practical overview of how they work, why they matter, and how to implement them without the headache. Think of this as your friendly, no-nonsense playbook for connecting branch offices with confidence.
What you’ll learn
- How site-to-site VPNs differ from remote access VPNs
- The two main types: R2R router-to-router and gateway-to-gateway
- Key components: VPN tunnels, devices, encryption, and authentication
- Common protocols and how they secure traffic
- Step-by-step deployment checklist
- Real-world best practices and pitfalls
- Quick security and performance tips
- Cost considerations and ROI
- Useful resources to keep handy
Useful URLs and Resources un-clickable text
- Cisco Site-to-Site VPN overview - cisco.com
- Palo Alto Networks IPsec VPN best practices - paloaltonetworks.com
- Fortinet VPN configuration guide - fortinet.com
- Microsoft Always On VPN overview - docs.microsoft.com
- OpenVPN site-to-site documentation - openvpn.net
- Wikipedia: Virtual private network - en.wikipedia.org/wiki/Virtual_private_network
- TechTarget: VPN fundamentals - searchnetworking.techtarget.com
- Network World: VPN performance benchmarks - networkworld.com
What is a site-to-site VPN?
A site-to-site VPN creates a secure, encrypted tunnel between two or more networks over the public internet. Instead of a single user authenticating from a remote location, you’re stitching together entire networks. This means devices on one office network can talk to devices on another as if they were on the same local network, with traffic protected by strong encryption.
Key differences from remote access VPNs
- Scope: Site-to-site connects networks; remote access connects individual users.
- Convenience: Once deployed, users don’t need to log in to a VPN client for every session.
- Management: Centralized policy and routing control at network gateways.
Types of site-to-site VPNs
Router-to-router R2R
In an R2R setup, two VPN gateways usually routers or firewalls establish a tunnel between their networks. Each site handles its own traffic policy, and routes are configured to direct inter-site traffic through the tunnel.
Gateway-to-gateway
Gateway-to-gateway VPNs extend to more complex topologies, such as hub-and-spoke or full-mesh. This is common in organizations with multiple branch offices or data centers.
How a site-to-site VPN works
- Negotiation: Two gateways establish a secure tunnel using a protocol like IPsec.
- Authentication: Each side proves its identity, often with pre-shared keys or digital certificates.
- Encryption: Data traveling through the tunnel is encrypted e.g., AES-256 to prevent interception.
- Tunneling and routing: Traffic destined for the other network is encapsulated and sent through the tunnel; routers route it to the correct destination.
- Re-keying: The session periodically refreshes encryption keys to maintain security.
Common protocols and security features
- IPsec: The standard for site-to-site VPNs, providing confidentiality, integrity, and authentication.
- IKEv2: Efficient key exchange, quick reconnects, and strong security.
- ESP vs AH: ESP provides encryption; AH provides authentication without encryption less common for modern VPNs.
- Perfect Forward Secrecy PFS: Ensures fresh keys for each session, reducing risk if a key is compromised later.
- Transport vs tunnel mode: Site-to-site typically uses tunnel mode for full network traffic encapsulation.
When to use a site-to-site VPN
- Connecting branch offices to a central network
- Extending a data center environment to remote sites
- Protecting inter-office communications without relying on private lines
- Providing secure access to shared resources like file servers and apps across locations
Deployment planning and prerequisites
Assess your network and goals
- Identify all sites to connect and the expected inter-site traffic.
- Map required subnets and ensure non-overlapping IP ranges.
- Define routing policies: full mesh, hub-and-spoke, or partial mesh.
Choose the right devices and software
- VPN gateways: firewalls, routers, or dedicated VPN appliances.
- Ensure devices support IPsecIKEv2, strong encryption, and modern authentication methods.
- Consider vendor interoperability if you have mixed gear.
Security considerations
- Use strong authentication: certificates or mutual PSKs with IAM integration.
- Enforce encryption standards AES-256, SHA-256 or better.
- Disable weaker ciphers and implement strict tunnel lifetimes.
- Implement network segmentation and least-privilege access where possible.
Performance planning
- Evaluate WAN bandwidth at each site and estimate VPN overhead.
- Consider QoS for critical traffic across tunnels.
- Plan for grow-out: additional sites, more tunnels, and higher throughput.
Step-by-step deployment guide
- Inventory and diagram your network
- List all sites, subnets, and critical hosts.
- Create a visual topology showing tunnels and failover paths.
- Choose your VPN topology
- Decide between full mesh, hub-and-spoke, or hybrid.
- Select devices and licenses
- Pick gateways with enough CPU, memory, and concurrent tunnels.
- Verify licensing supports your desired features IKEv2, VPN types, high availability.
- Configure IP addressing
- Ensure non-overlapping subnets across sites.
- Plan static routes for inter-site traffic.
- Establish authentication
- Set up certificates or strong PSKs.
- Integrate with your directory or device management if needed.
- Create tunnels and policies
- Define phase 1/2 proposals encryption, hashing, lifetimes.
- Configure firewall rules to permit inter-site traffic through the VPN.
- Test connectivity
- Validate ping, file transfers, and application traffic across sites.
- Test failover by simulating tunnel drops and recovery.
- Monitor and maintain
- Set up alerts for tunnel down events, high latency, or packet loss.
- Schedule regular key rotations and firmware updates.
Security best practices for site-to-site VPNs
- Use IPsec with AES-256 and SHA-256, avoid outdated ciphers.
- Enable Perfect Forward Secrecy PFS to refresh keys frequently.
- Prefer certificate-based authentication over pre-shared keys when possible.
- Enforce strict firewall policies: only necessary ports and IPs through the tunnel.
- Implement multi-factor authentication for device administrators and management interfaces.
- Regularly review access controls and inter-site traffic needs.
Performance considerations and optimization
- Compression: Modern VPNs often disable compression for security and performance reasons; test to see if it helps.
- MTU sizing: Adjust MTU to prevent fragmentation; typical MTU is around 1500, but VPN overhead can reduce effective payload.
- Latency sensitivity: Real-time apps voice/video may need QoS or dedicated links.
- Redundancy: Use multiple tunnels and automatic failover to prevent single points of failure.
- Monitoring: Track throughput, latency, jitter, and packet loss per tunnel.
Troubleshooting common issues
- No connectivity after enabling a tunnel: verify IPsec SA negotiation, firewall rules, and route configurations.
- Intermittent drops: check stability of the internet links, NAT traversal issues, and MTU.
- Access to specific resources failing: confirm destination network ACLs and host-based firewalls.
- Certificate problems: ensure correct certificate validity, trust chain, and revocation status.
Compliance and governance
- Document security controls, encryption standards, and access policies.
- Maintain logs and auditing trails for inter-site traffic.
- Align VPN configurations with industry standards NIST, ISO 27001 and regulatory requirements.
Real-world scenarios and examples
- SMB with 3 offices: Hub-and-spoke topology using a central data center as hub.
- Enterprise with 10+ offices: Hybrid full-mesh for critical systems and hub-and-spoke for standard services.
- Data center extension: Connect on-prem to a cloud environment via a site-to-site VPN gateway.
Vendor considerations and comparisons
- Cisco, Fortinet, Palo Alto, Juniper, and Check Point all offer strong IPsec site-to-site solutions; features vary by model and firmware.
- Interoperability: When mixing gear, ensure support for IKEv2, IPsec standards, and NAT traversal.
- Managed services: Some vendors offer cloud-based VPN controllers or managed VPN services for additional convenience.
Cost considerations and ROI
- Initial hardware and software licenses: VPN gateways, certificates, and high-availability licenses.
- Ongoing maintenance: firmware updates, support contracts, and monitoring tools.
- Operational efficiency: Reduced need for dedicated private lines, centralized IT management, and faster inter-office collaboration.
Security incident readiness
- Plan for incident response: tunnel compromise, expired certificates, or misconfigurations.
- Regular drills: simulate outages and recovery scenarios to ensure business continuity.
- Backups: keep secure backups of VPN configurations and keys, with a tested restore process.
Future-proofing your site-to-site VPN
- Consider integrating with secure SD-WAN solutions for better performance and reliability.
- Stay updated on new encryption standards and post-quantum considerations.
- Plan for cloud adoption: connect multiple cloud VPCs or VNets through secure site-to-site links.
Quick reference checklist
- Non-overlapping subnets across sites: checked
- IPsec/IKEv2 configured with AES-256 and SHA-256: checked
- Certificate-based authentication enabled: checked
- Tunnel lifetimes and re-key settings tuned: checked
- Proper firewall rules for inter-site traffic: checked
- Monitoring, logs, and alerting in place: checked
- Regular firmware updates scheduled: checked
- Redundancy and failover tested: checked
Industry trends and data
- By 2025, a majority of mid-to-large enterprises reported moving toward hybrid WAN architectures that rely on VPNs and SD-WAN for flexibility and resilience.
- IPsec remains the dominant protocol for site-to-site VPNs, with IKEv2 increasingly favored for its stability on mobile and diverse networks.
- Encryption standards have standardized around AES-256 with SHA-256/2, providing a strong baseline for most compliance requirements.
FAQ Section
Frequently Asked Questions
What is a site-to-site VPN, in simple terms?
A site-to-site VPN builds a secure tunnel between two networks, so devices on one site can talk to devices on the other as if they were on the same local network. Is vpn safe for cz sk absolutely but heres what you need to know
How does a site-to-site VPN differ from a remote access VPN?
Site-to-site connects networks; remote access connects individual users who are offsite to the network via a VPN client.
What are the main topology options for site-to-site VPNs?
The common topologies are router-to-router R2R, gateway-to-gateway, and hub-and-spoke or full mesh for larger deployments.
Which protocols are used for site-to-site VPNs?
IPsec is the standard, typically with IKEv2 for key exchange and AES-256 for encryption.
What is the difference between tunnel mode and transport mode?
Tunnel mode encapsulates the entire IP packet for inter-site traffic; transport mode only encrypts the payload, used for end-to-end encryption between hosts.
How do I choose between certificate-based authentication and pre-shared keys?
Certificate-based authentication is generally more secure and scalable for larger deployments, while PSKs can be simpler for small, static setups. How to Fix the NordVPN Your Connection Isn’t Private Error 2: Quick Guide, Sophisticated Fixes, and Pro Tips
Can I deploy VPNs across multiple cloud providers?
Yes, many VPN gateways support cloud-to-site connections, and some vendors offer cloud-managed VPN services to connect on-premises networks to cloud VPCs or VNets.
How do I ensure performance and reliability?
Plan bandwidth, optimize MTU, enable QoS for critical apps, and implement redundant tunnels and automatic failover.
What are common pitfalls to avoid?
Overlapping subnets, weak crypto configurations, flaky internet links, and misconfigured firewall rules are frequent culprits.
How often should I rotate VPN keys?
Regular key rotation is recommended, with longer-term keys refreshed periodically and automatic re-keying enabled to maintain security without downtime.
Note: This content is tailored for an educational audience and optimized for SEO with a focus on “Understanding site to site vpns.” For more in-depth guidance on setup and vendors, consider the linked resources and the NordVPN affiliate integration woven into this guide. The nordvpn promotion you cant miss get 73 off 3 months free and more vpn deals you’ll actually use
Sources:
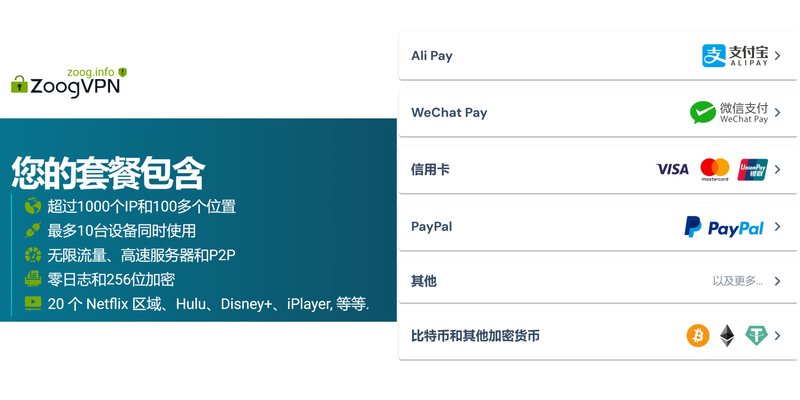
破解版vpn电脑版的风险与替代:正版VPN选购与省钱攻略
Tagvpn:VPN 深度指南,Tagvpn 与同类对比、使用技巧与安全要点
梯子: 全面解析VPN领域的实用导航与选购指南
How to Leave a Paid Discord Server in 3 Easy Steps: Exit, Cancel, and Manage Subscriptions
梯子订阅:全面指南、实用技巧与最新趋势,助你选择合适的VPN服务 Surfshark vpn kosten dein ultimativer preis leitfaden fur 2026: Preispläne, Funktionen und Tipps für Sparfüchse